In the realm of secure and efficient servers management, one aspect stands out — SSH keys. If you want to make your VPS more secure while making access easier, you need to know how to pair an SSH key with it.
SSH (Secure Shell) keys provide a robust authentication method that not only enhances security but also simplifies the login process, eliminating the need for cumbersome passwords.
In this guide, I will show you how to pair SSH keys with your VPS. This tutorial will give you the knowledge and skills you need to connect your local machine to your virtual server.
So, let's embark on the journey to mastering the art of SSH key pairing and take control of your VPS with confidence!
What are SSH Keys
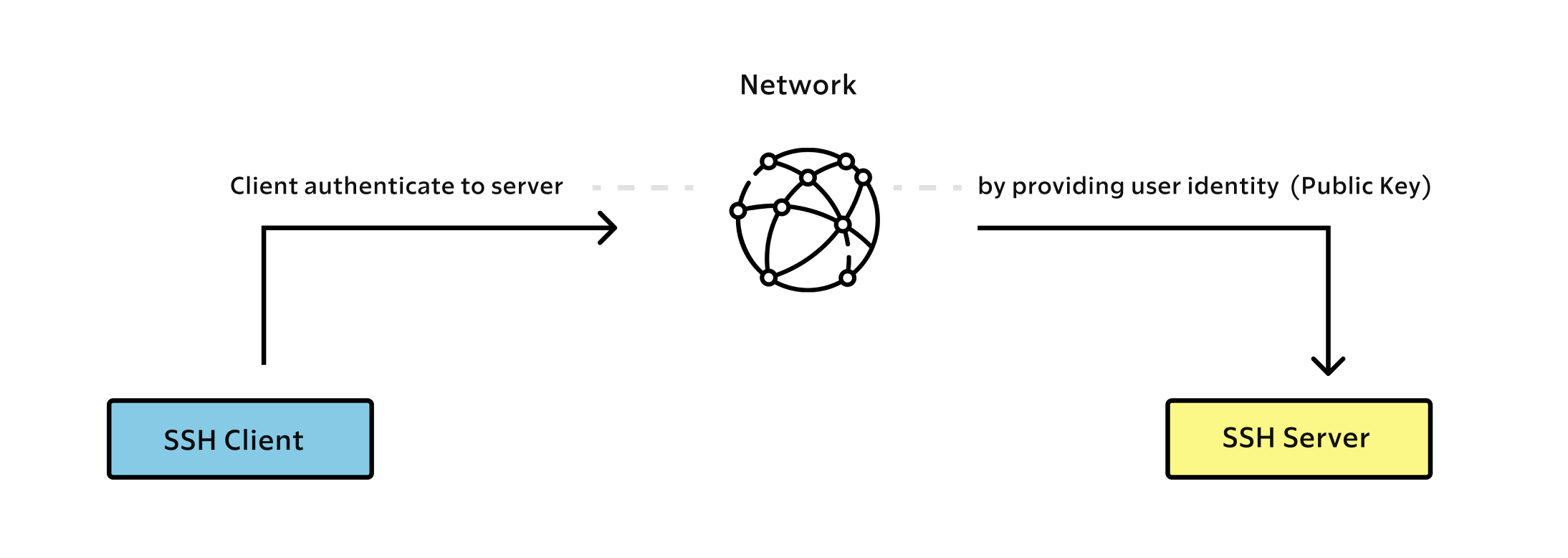
SSH keys are a pair of cryptographic keys used to authenticate and secure communication between two parties over a computer network. The SSH (Secure Shell) protocol is commonly used for secure remote access to systems and for secure file transfers.
Generating SSH Key Pair
On your computer, navigate to the ~/.ssh directory, use the cd command to navigate to the ~/.ssh directory, which is the standard location where SSH keys are stored on Linux systems (macOS included).
$ cd ~/.ssh
Use the ssh-keygen command to generate a new SSH key pair. If you're generating an SSH key for the first time, you'll be asked to enter a path for the key files, which should be ~/.ssh/id_ed25519 for the private key and ~/.ssh/id_ed25519.pub for the public key.
You'll also be asked if you want to set a passphrase for the private key. It will also ask you to a set a passphrase for enhanced security, but if you’re not sharing your computer with someone else, you can just press enter.
When you use a passphrase-protected key, even if someone gains access to your private key file, they would still need to know the passphrase to use the key.
Without a passphrase, if someone obtains your private key, they can use it immediately to authenticate to any system where you've deployed the corresponding public key. Adding a passphrase helps mitigate this risk.
That being said, you can run the following command to generate your SSH-keys:
$ ssh-keygen -t ed25519
The output will look like the sample below:
Your identification has been saved in /home/username/.ssh/id_rsa.
Your public key has been saved in /home/username/.ssh/id_rsa.pub.
The key fingerprint is:
SHA256:CAjsV9M/tt5skazroTc1ZFREAz+kGtYUIPhRvvZJYBs username@hostname
The key's randomart image is:
+---[RSA 3072]----+
|o ..oo.++o .. |
| o o +o.o.+... |
|. . + oE.o.o . |
| . . oo.B+ .o |
| . .=S.+ + |
| . o..* |
| .+= o |
| .=.+ |
| .oo+ |
+----[SHA256]-----+
Add Your Public Key to Your VPS
While still in the terminal, use the following command to view your newly created public key. If you gave the key a name other tan default replace “id_ed25519” with the name you chose.
$ cat ~/.ssh/id_ed25519.pub
You will see the key’s content, which may look something like this
ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIK0wmN/Cr3JXqmLW7u+g9pTh+wyqDHpSQEIQczXkVx9q username@hostname
Select all the displayed content, which usually starts with ssh-ed25519 and ends with your username@hostname.
Alternatively, you can use the following command to copy the content of your public key
$ pbcopy < ~/.ssh/id_ed25519.pubNow connect to your VPS using a login and password, you can use the ssh command.
Here's the basic syntax:
$ ssh username@your_server_ip
Replace username with your VPS username and your_server_ip with the actual IP address or domain of your VPS.
When you run this command, you will be prompted to enter your password for the specified user. After providing the correct password, you should be logged in to your VPS.
Now go to your ssh folder in your VPS (If it doesn’t exist, create it with mkdir -p ~/.ssh)
$ cd ~/.sshNow you can create or modify the authorized_keys file within this directory, and add the content of the id_ed25519.pubat the end of this file.
$ echo public_key_string >> ~/.ssh/authorized_keysIn the above command, substitute the public_key_string with the output from the cat ~/.ssh/id_rsa.pub command that you executed on your local system.
There we go! Now let’s move to the next step.
Disabling Password Authentication on your VPS
This step will lock down password-based logins, so ensuring that you will still be able to get administrative access is essential.
Once the above conditions are true, open the SSH daemon’s configuration file:
$ sudo vim /etc/ssh/sshd_config
Inside the file, search for a directive called PasswordAuthentication. This may be commented out. Uncomment the line by removing any # at the beginning of the line, and set the value to no. This will disable your ability to log in through SSH using account passwords:
$ PasswordAuthentication no
Save and close the file opened on vim with this command /wq or /wq! once you have finished. To actually implement the changes you just made, you must restart the service.
$ sudo systemctl restart ssh
After completing this step, you’ve successfully configured your SSH daemon to only respond to SSH keys.
Connect to your VPS with SSH
Now that you have configured the SSH identity files and disabled the password auth on your server, you can connect to your VPS with this command:
$ ssh -i ~/.ssh/id_ed25519 <username>@<your_server_ip>
Conclusion
You should now have SSH key-based authentication configured and running on your server, allowing you to sign in without providing an account password.
Connecting to a server through SSH with key-based authentication rather than password authentication offers several security advantages. Here are some reasons why using SSH keys is considered more secure:
- Stronger Authentication
- Protection Against Brute Force Attacks
- Elimination of Password-Based Vulnerabilities
- Improved Resistance to Phishing
- Reduced Need for Passwords
- Logging and Auditing
In summary, SSH key-based authentication provides a more secure and robust method of connecting to servers compared to password authentication. It is a fundamental security best practice to use SSH keys wherever possible to protect your systems from unauthorized access and potential security threats.
If you want to find out more about the pitfalls and disadvantages of using password authentication, take a look at this article.
🔍. Similar posts
How to Use Custom Hooks in React
01 Jun 2025
Understanding Stale Values in React
17 May 2025
Write Cleaner and Faster Unit Tests with AssertJ as a Java Developer
12 May 2025